Blog
Understanding Saudi Arabia's NDMO Standards
By Chris Brook on Wed, 10/02/2024
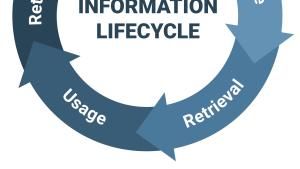
As governments transition to fully digital records, protecting sensitive data has become a critical priority. In the Middle East, Saudi Arabia is leading the way with its National Data Management and Personal Data Protection Standards.